Lets go back to early 90’s Street Fighter series is churning arcades up there and fans of fighting games have gone berserk with the offering of Capcom,enter
Prologue
SNK's King of Fighters has been touted as the reboot of the series,to restore it to its former glory,this theme emerged from the game’s brand new style of characters and sprites which contribute to the overall visual overhaul of the series in ages,and to do what Street Fighter 4 did to the Street Fighter series.However to my dismay,this game is a disappointment.This 3 on 3, 2D fighter sports a fairly solid fighting engine much like the older KOF’s but everything surrounding that engine is either lackluster or broken. Or both. It's a shame that the one game aimed at the rebirth of a dying franchise has been rushed and lacks developer effort.
Characters
As we all know,the characters are the core of the fighting game,after all they provide an identity to the game.KOF sports all the nostalgic and series stars –Terry Bogard,Kim Kaphwan,Iori yagami and more ..however series iconic Mai Shirunai is missing (I miss her hot figure :P). 
Gameplay,Graphics and presentation
It follows the old school rules of the series,every character has a Light Punch, Heavy Punch, Light Kick and Heavy Kick. These form the basic attacks and you can combine them to execute all orts of complex combos. By Pressing both Light Punch and Light Kick you can evade an attack while you can execute a by hitting both punch buttons.You can block heavy attacks by Hitting both heavy attacks which can knock your opponent away and give your fighter some room to breathe.You can parry an incoming strike by hitting heavies while holding D-Pad which will perform a Guard Attack.

As with all fighting games,every character has his set of specials and super moves.one of new systems KOF introduces is the Critical Counter system. Fill up your gauge during a sparring session and, once filled, counter your opponent's attack with a Heavy Punch or Heavy Kick,which will activate a special combo state where you can release all sorts of combos and chain attacks together.It was a real blast (I like real damage).
When it comes to selecting stages,I was disappointed with the fact that there are only six stages to choose from, two of which are just day/night variations of each other. And there is just one soundtrack for the whole game !!!! Cant they tune it all together ?
The core battle system in KOFXII is faithful to the series however it feels bland when compared to Street Fighter 4,BlazBlue and Guilty Gear series.The new character animation are praiseworthy,but there are resolution issues,as they seem to be pixilated when the combat starts.
Modes
KOFXII can be quite fun when you mash it out with your friend locally,but it has got some serious issues on both the PS3 and 360. No unlockables,just 2 modes –arcade and multiplayer,no story and survival modes..well,WHAT WERE THEY THINKING?!! The game navigation system is broken, For example, you can't back out of the character selection screen once you dive in, the game loads at odd points during menu navigation and the training mode lacks a "reset" button.
Multiplayer
LAG LAG LAG..that's what I can describe the KOF12 multiplayer as of now,the online multiplayer is unplayable.They released patches but they too suffered from horrendous lags,and in short,it ruins the multiplayer experience as most player nowadays match their skills online. Also the patch they made me (forcefully and I M SERIOUS !!!) to install was an odd 700+ MB file that installs and updates game data which you would normally install from the disc. one more act of dev-foolishness..
Epilogue
King of Fighters XII is fun to play when you're fighting a buddy locally, but everything else about the game is seriously lacking. This is not rebirth you have been waiting for and SNK was hoping for, as just smoothly animated sprites can't make a lackluster game with broken online support a topdog.I would rather recommend you to get your hands on Blazblue,play Street Fighter 4 and wait for Tekken 6 if you are a hardcore fighting fan.
Final Score – 27/40
Posted by XERO .ALL RIGHTS RESERVED.


 Security Expert. I will then go for CEH and will be a
Security Expert. I will then go for CEH and will be a 

 crappy graphics, bad controls with no mouse support and worse no dynamic lighting. It was a crappy port of an excellent game. Ubisoft ported Capcom's prized baby on PC and I thought they made it like something only monkey's can play.
crappy graphics, bad controls with no mouse support and worse no dynamic lighting. It was a crappy port of an excellent game. Ubisoft ported Capcom's prized baby on PC and I thought they made it like something only monkey's can play.
 them and ask me with a nag screen to purchase the full version.But then there were times when I wanted to create my own screensavers,and I did that with Easy 3D Creator.Easy 3D creator is a
them and ask me with a nag screen to purchase the full version.But then there were times when I wanted to create my own screensavers,and I did that with Easy 3D Creator.Easy 3D creator is a 
 be one,and its your interest,your passion,your mindset which will drive you to be one.A hacker evolves from many stages,from the lower level script kiddie to the elite level Guru,one needs to be in constant research to develop their soft and hard skills.I m myself learning a lot,and I would like to share 5 Hacking sites,which you must visit,if you want to be an expert in
be one,and its your interest,your passion,your mindset which will drive you to be one.A hacker evolves from many stages,from the lower level script kiddie to the elite level Guru,one needs to be in constant research to develop their soft and hard skills.I m myself learning a lot,and I would like to share 5 Hacking sites,which you must visit,if you want to be an expert in  compression and file storage algorithms but a relatively less known compatibility feature of
compression and file storage algorithms but a relatively less known compatibility feature of  Null Byte exploit.Almost all forums include a picture and avatar uploading system where you can upload your user signatures and avatars.At first look it looks like a normal uploading system,but its a way to upload our own files into forum,or to get into admin area and literally “OWN” the forum. However as this hack is outdated as of now,most have deployed some form of input sanitation to prevent such an attack. Nevertheless,thousands of vulnerable forums do exists even now with even some bigger names crossed here.
Null Byte exploit.Almost all forums include a picture and avatar uploading system where you can upload your user signatures and avatars.At first look it looks like a normal uploading system,but its a way to upload our own files into forum,or to get into admin area and literally “OWN” the forum. However as this hack is outdated as of now,most have deployed some form of input sanitation to prevent such an attack. Nevertheless,thousands of vulnerable forums do exists even now with even some bigger names crossed here. beginning of the end for the reign of Microsoft and there are others who say that Google will fall flat on its face and fail. Without more specifics only time will say for sure how big of a splash the OS will really make. Google pledges to release more information regarding the OS later this summer.
beginning of the end for the reign of Microsoft and there are others who say that Google will fall flat on its face and fail. Without more specifics only time will say for sure how big of a splash the OS will really make. Google pledges to release more information regarding the OS later this summer.  sold through the App Store, Apple iPhone is becoming a new platform for gaming and traditional game developers are beginning to see its potential in a big untapped market. And porting titles like RE4 and MGS4 on iPhone proves it. Resident Evil 4 is one of the most successful and intricately detailed games of all time which pushed a struggling franchise to the pinnacle of its genre.We might be seeing
sold through the App Store, Apple iPhone is becoming a new platform for gaming and traditional game developers are beginning to see its potential in a big untapped market. And porting titles like RE4 and MGS4 on iPhone proves it. Resident Evil 4 is one of the most successful and intricately detailed games of all time which pushed a struggling franchise to the pinnacle of its genre.We might be seeing 


 combines the fast gameplay of a fighting game with intuitive controls and has made its place in our hearts since last 10 years.Its a Chibi styled fighting game which combines the retro anime feel and you fight with against computer or a friend,head to head or in a melee.
combines the fast gameplay of a fighting game with intuitive controls and has made its place in our hearts since last 10 years.Its a Chibi styled fighting game which combines the retro anime feel and you fight with against computer or a friend,head to head or in a melee. 
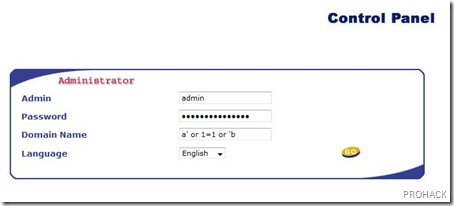
 4.4 have a SQL injection vulnerability in them which makes their Admin control panel easily accessible,and I mean in one big shot,you will be admin of that site.
4.4 have a SQL injection vulnerability in them which makes their Admin control panel easily accessible,and I mean in one big shot,you will be admin of that site.

 friendliness by the guys at
friendliness by the guys at 
 it was the right time to rip off the tag,and they did it.Further,with the world going mobile,they took some of the steps to better enhance the
it was the right time to rip off the tag,and they did it.Further,with the world going mobile,they took some of the steps to better enhance the 
 movies..and you can do that too. Well its done using ARP Poisoning..Sounds geeky but its the technical name of network sniffing.Basically,sniffing is used to get passwords – encrypted or unencrypted in a network. But it can also be used to choke the network bandwidth and getting maximum bandwidth in a single system. For those who don't know how it happens,lemme give you a little insight on how it happens.
movies..and you can do that too. Well its done using ARP Poisoning..Sounds geeky but its the technical name of network sniffing.Basically,sniffing is used to get passwords – encrypted or unencrypted in a network. But it can also be used to choke the network bandwidth and getting maximum bandwidth in a single system. For those who don't know how it happens,lemme give you a little insight on how it happens.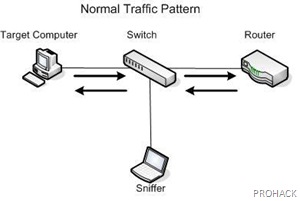

 To do this, Download Ettercap and poison the network (shift + U then control + S ..do some homework and get the idea) but DONT START SNIFFING.Once you have poisoned it,you will be able to
To do this, Download Ettercap and poison the network (shift + U then control + S ..do some homework and get the idea) but DONT START SNIFFING.Once you have poisoned it,you will be able to  web got me an acceptable solution,and I got WMLBROWSER extension for Firefox.This
web got me an acceptable solution,and I got WMLBROWSER extension for Firefox.This 
 anything.Well,this time I will be briskly shedding some light on the Top 5 Power graphic cards money can buy (for the time being) for serious gamers (and not so serious gamers) out there. Couple these monsters with monster CPU from Intel,ferocious board from Nvidia/ATi/Intel,hook them up with a superb cooling solution,upgrade your power supply and you are set to game like anything. Trust me..
anything.Well,this time I will be briskly shedding some light on the Top 5 Power graphic cards money can buy (for the time being) for serious gamers (and not so serious gamers) out there. Couple these monsters with monster CPU from Intel,ferocious board from Nvidia/ATi/Intel,hook them up with a superb cooling solution,upgrade your power supply and you are set to game like anything. Trust me..



 any other brand,the technology remains same and provides whackers (wireless malicious hackers) new playground for their experiments.In this article,I will be listing some Bluetooth tools for security – both breaking and making.
any other brand,the technology remains same and provides whackers (wireless malicious hackers) new playground for their experiments.In this article,I will be listing some Bluetooth tools for security – both breaking and making. It features Bluetooth address spoofing,socket shells like AT and RFCOMM and also implements tools like L2CAP packet generator and connection resetter and RSCOMM scanner which are a must for any Bluetooth security enthusiastic.
It features Bluetooth address spoofing,socket shells like AT and RFCOMM and also implements tools like L2CAP packet generator and connection resetter and RSCOMM scanner which are a must for any Bluetooth security enthusiastic.


 It can deep scan all services of your Bluetooth device using this software.
It can deep scan all services of your Bluetooth device using this software.