Recently, i tried to have a paradigm shift of some sort, to move from ASM to web technologies, 
The results ? well, I found some vulnerabilities in some prominent sites which I am disclosing here..,the deal is that I tried to contact the vendors (more on this later) to notify them of vulns. Remember hackable government & educational websites, consider this as the spiritual follow-up of the article.
Disclaimer
I HAVE NOT HACKED ANY OF THE SITES AND THEIR DATABASES IN ANY WAY,JUST TESTED WEBSITES FOR VULNERABILITIES. I TESTED THEM AND FOUND ERRORS WHICH MAY/MAY NOT BE DISCLOSED HERE AND IN NO WAY ANY ONE CAN SUE ME FOR THIS AS I DID AND MEANT NO HARM TO THE DATA OF CONCERNED ORGANIZATIONS.
BY READING THIS ARTICLE YOU AGREE WITH THE DISCLAIMER.
IF YOU AGREE WITH THIS AGREEMENT,CONTINUE READING ELSE IMMEDIATELY LEAVE THIS WEBSITE.
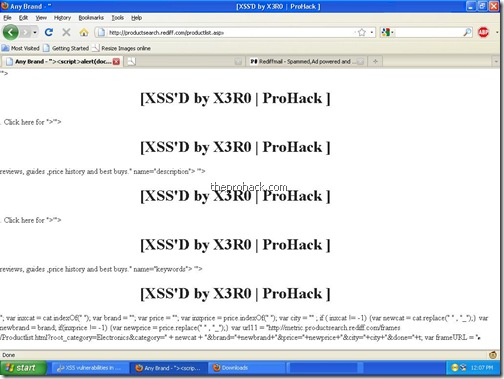
Here we go, it all started with www.in.com [ ALEXA RANK 298 ] which had a simple XSS vulnerability to display cookies , inject code & God knows what else, I tried to contact the technical team in vain, then contacted them via a simple feedback form. Waiting for their response as of now..I moved on then. Please note that I have censored all the URLs & script details so as to protect attack originating after this article :P

I never liked Rediff [ ALEXA RANK 128 ] & their services..too much ads to digest for me, again, it was easy to inject .
dl4all.com [ ALEXA RANK 1517 ] was no exception, a simple search & thats all.

shaadi.com [ ALEXA RANK 935 ] the premium matrimonial portal of India has XSS flaws..


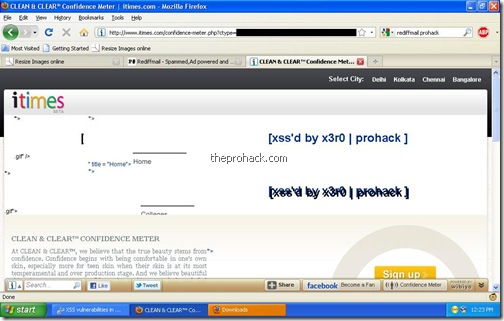
A leading social networking website Itimes.com [ ALEXA RANK 6024 ] was no better & a nobrainer.
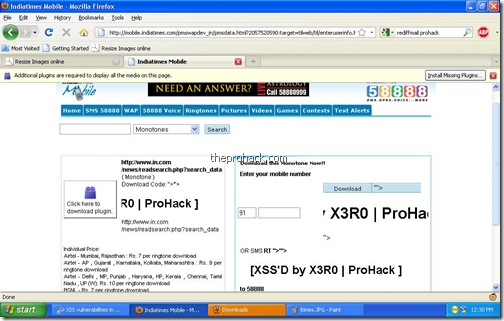
Indiatimes.com [ ALEXA RANK 168 ] anyone ?
enough..as expected, I tried to contact all the support staff before releasing this article. My point ? what happens when there is no competent technical staff to handle the issue (I am looking at you AXISBANK !) have a look at it

great..now that's what we wanted..more flaws in “secure” websites which pledge for our privacy. For the record, XSS flaws are independent of encryption & the so called layman lock mechanisms as the application behavior remains the same. I tried to contact authorities at AXIS bank but they were asking for my bank account number, to contact nodal officer, to contact xyzabc blah blah..but no support / tech staff.
Lets have a look at the alexa rank of the above websites -
www.rediff.com - 128
www.In.com - 298
www.Indiatimes.com - 168
www.shaadi.com – 935
www.dl4all.com – 1517
www.axisbank.com - 2330
www.itimes.com – 6024
again, the above sites are the head honchos of social networking, downloads, have a lot of data in their hands & are vulnerable to XSS. Why they still have no technical feedback team is beyond my belief. Except itimes, i wasn't able to find a bug reporting facility in any of the sites mentioned above. Now that's pure genius ! Just what were they thinking ?!! Cant they learn from some good examples ?
what i am doing ? to quote Rsnake
“ How many compromises of data security, that you are aware of, have been disclosed to the public as a percentage? “
ditto here..the websites are not safe, & so their claims. It took me about 30 minutes to write this post including the time to try XSS on the websites, ( excluding the email contact with the authorities where possible ). XSS/CSRF is the modern nightmare of security for any website today, prominent websites are constantly under attack & the recent cases which i have heard as of now, lot of bank websites were targets of CSRF based attacks, phishing & XSS. Imagine what a skillful attacker can do with a lot of time & patience (& a reason perhaps).
pray & spray..& trust no one.
like this post ? you can buy me a beer :)
Posted by XERO. ALL RIGHTS RESERVED

Great Work Sir
ReplyDelete