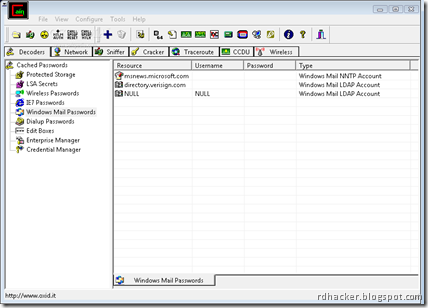
Cain & Abel is a password recovery tool for Microsoft Operating Systems. It allows easy recovery of various kind of passwords by sniffing the network, cracking encrypted passwords using Dictionary, Brute-Force and Cryptanalysis attacks, recording VoIP conversations, decoding scrambled passwords, recovering wireless network keys, revealing password boxes, uncovering cached passwords and analyzing routing protocols. The program does not exploit any software vulnerabilities or bugs that could not be fixed with little effort. It covers some security aspects/weakness present in protocol's standards, authentication methods and caching mechanisms; its main purpose is the simplified recovery of passwords and credentials from various sources, however it also ships some "non standard" utilities for Microsoft Windows users.
Cain & Abel is a useful tool for network administrators, teachers, security consultants/professionals, forensic staff, security software vendors, professional penetration tester and everyone else that plans to use it for ethical reasons.
The latest version is faster and contains a lot of new features like APR (Arp Poison Routing) which enables sniffing on switched LANs and Man-in-the-Middle attacks. The sniffer in this version can also analyze encrypted protocols such as SSH-1 and HTTPS, and contains filters to capture credentials from a wide range of authentication mechanisms. The new version also ships routing protocols authentication monitors and routes extractors, dictionary and brute-force crackers for all common hashing algorithms and for several specific authentications, password/hash calculators, cryptanalysis attacks, password decoders and some not so common utilities related to network and system security.
Posted by XERO . OXID.IT. ALL RIGHTS RESERVED.
Will this work on facebook
ReplyDeleteyes i does...
ReplyDeleteWorks well thanks!
ReplyDeleteCan I use it to find the password of an account on a specific site?
ReplyDeleteouyhn
ReplyDeletebut trouble is when i run arp poisoning . . . after much much time it gives me no result just poisoning poisoning . . . any solution !!!
ReplyDeletei need to know how to use cain and abel to get a wireless router password? is it possible or am i waisting my time?
ReplyDeleteWhere do I find info on how to use cain & able to find out what someone's wireless net wep or wpa password is. I do not have a connection to their network
ReplyDeleteyou have to go to the "apr-dns" tab at the left. then you click the blue plus sign. then type in the url of the site the user wants to go to. then click resolve and type the url of the site YOU want the user to go to. then click ok and then ok again. now it should be rerouting the traffic from the site the user wants to go to, to the site you want the user to go to.
ReplyDelete