Ah…Linux..The pinnacle of what open source can achieve today..the brainchild of Linus Torvalds has surely come a lot  further and evolved to show the world what it is capable of.As an extremely reliable Operating system, Linux rarely needs to be rebooted. But when it does, it’s often slow to boot.Loads of Matrix style lines scrolling down the screen are sure to drive nuts added with boot time of GUI initialization.. Fortunately, there are ways to speed things up. Some of these methods are not terribly difficult. (although some, unfortunately, are). Let’s take a look at Top 10 Speed hacks of Linux and let your linux box reincarnate with speed.
further and evolved to show the world what it is capable of.As an extremely reliable Operating system, Linux rarely needs to be rebooted. But when it does, it’s often slow to boot.Loads of Matrix style lines scrolling down the screen are sure to drive nuts added with boot time of GUI initialization.. Fortunately, there are ways to speed things up. Some of these methods are not terribly difficult. (although some, unfortunately, are). Let’s take a look at Top 10 Speed hacks of Linux and let your linux box reincarnate with speed.
[1]. Quick Fixes - Disable unnecessary services 
Linux comes in various flavors bundled with a lot of applications.However,most of us don't even use Linux to its full potential. Depending upon the use of the machine, plenty of services and running programs won’t be needed. And if you are using Linux just for a desktop,then you won’t be needing the default sendmail , httpd, and many other services.You can also turn off many other services if your Linux box is used as a small web server by going to Administration menu,tweaking the Services entry and deselect all of the services you don’t want to start.
[2]. Free up Your Kernel - Disable unnecessary kernel modules
If your Linux box is wired to the LAN/Ethernet,then you don’t need to have a wireless kernel module loaded. More services like smartcard modules and more can be disabled and the load can be taken off from the kernel.This task is a bit  difficult requires recompilation of kernel, which is daunting for even the *inux geeks. To do this, you will need the kernel sources and then follow the standard steps for compiling a kernel. You will be having a ride through the internals of your system just disable all of the kernel modules you don’t need.
difficult requires recompilation of kernel, which is daunting for even the *inux geeks. To do this, you will need the kernel sources and then follow the standard steps for compiling a kernel. You will be having a ride through the internals of your system just disable all of the kernel modules you don’t need.
For added safety,install Bootchart which will tell you if Kernel modules are properly installed and running on your system. Not only will this give you a good list of modules, it will illustrate for you what is happening during your system boot. You can also issue the command
chkconfig –list | grep 3:on
to find out what services are running. Once you know what loading modules you don’t need, you can remove them during a kernel recompilation. While you’re at it, compile the kernel to exactly match your architecture. 
[3]. Take Load Off Linux - Use a lightweight window manager instead of GNOME or KDE
Using a smaller window manager drastically reduces graphical boot time. Instead of having to wait that extra 30 to 60 seconds for GNOME or KDE to boot up, why not wait two to 10 seconds for Enlightenment or XFCE to boot up? Not only will they save you boot time, they will save your memory and the headache of dealing with bloatware.
[4]. CUI ROKZ’ - Use a text-based login instead of a graphical login
The graphical logins do two things: increase load times and create headaches trying to recover from an X windows failure.Most of Linux machines which boot to run level 3 instead of run level 5 will halt at the text-based login, where you only have to log in and issue startx to start your desktop of choice.So CUI login is the way to go.
[5]. The Flying Penguin - Use a lighter Linux distribution 
Are You a Linux newbie ? Instead of loading the heavyweight SUSE, why not try a DSL, Puppy Linux, or Gentoo? The boot times for these smaller distributions are far faster than the more bloated Fedora (SUSE and even Ubuntu).Loading lighter linux distributions will save you from lot of headaches. Of the larger distributions, OpenSuSE claims to boot the fastest, but between the latest Fedora and Ubuntu, Ubuntu blows Fedora’s boot times away (and that is out of the box,trust me..).
[6]. Get Savvy - Use an OpenBIOS
If you’re tech savvy enough to upgrade your PC’s firmware, you might consider a migration to open source BIOS which  will allow Linux to actually initialize the hardware as it boots (instead of relying on the BIOS). Also, many open BIOSes can be customised to meet your machine’s specific needs. If you don’t go the open BIOS route, you can at least configure your BIOS to not search for a floppy drive that’s not there or to boot directly to the first hard drive (instead of the CD drive first).
will allow Linux to actually initialize the hardware as it boots (instead of relying on the BIOS). Also, many open BIOSes can be customised to meet your machine’s specific needs. If you don’t go the open BIOS route, you can at least configure your BIOS to not search for a floppy drive that’s not there or to boot directly to the first hard drive (instead of the CD drive first).
[7]. DHCP woes - Avoid dhcp
If you are working on a home network (or a small business network) where address lease isn’t a problem, go with static IP addresses. This will keep your machine from having to call out to a dhcp server to get an IP address. If you take this approach, make sure you configure your 
/etc/resolve.conf
to reflect your DNS server addresses as well.
[8]. Hotplug unplugged - If you can spare it, get rid of hotplug
Hotplug is the system that allows you to plug in new devices and use them immediately. If you know your server won’t need this system, delete it. This will cut down on boot time. On many systems, hotplugging consumes much of the boot time. Removing hotplug will vary depending upon the distribution you use.
NOTE: udev has, for the most part, replaced hotplug. But if you’re running an older distribution, this does apply. 
[9]. If you are REALLY daring, you could give initng a try
The initng system serves as a replacement for the sysvinit system and promises to drastically decrease boot times in UNIX-like operating systems. If you would like to see the initng system in action, you can give the Pingwinek livecd a try.
[10]. HackerPunk - Use a hack with Debian
If you’re using Debian, there is a simple hack you can use to switch your startup scripts to run in parallel. If you look at  the
the
/etc/init.d/rc
script, you will see:
CONCURRENCY=none
around line 24. Change this line to
CONCURRENCY=shell
and you should see a reduction in boot times.
Shall i say “Thats All Folks..” . Yep..thats it..thats the way it is. There are ofcourse better speed hacks available but the above ones shall cover pretty much everything.

So..Keep learning Folks
POSTED BY XERO.ALL RIGHTS RESERVED. TUX PACKAGES BROUGHT TO YOU BY CRYSTALXP.NET.


 further and evolved to show the world what it is capable of.As an extremely reliable Operating system,
further and evolved to show the world what it is capable of.As an extremely reliable Operating system, 
 difficult requires recompilation of kernel, which is daunting for even the *inux geeks. To do this, you will need the kernel sources and then follow the standard steps for compiling a kernel. You will be having a ride through the internals of your system just disable all of the kernel modules you don’t need.
difficult requires recompilation of kernel, which is daunting for even the *inux geeks. To do this, you will need the kernel sources and then follow the standard steps for compiling a kernel. You will be having a ride through the internals of your system just disable all of the kernel modules you don’t need. 

 will allow Linux to actually initialize the hardware as it boots (instead of relying on the BIOS). Also, many open BIOSes can be customised to meet your machine’s specific needs. If you don’t go the open BIOS route, you can at least configure your BIOS to not search for a floppy drive that’s not there or to boot directly to the first hard drive (instead of the CD drive first).
will allow Linux to actually initialize the hardware as it boots (instead of relying on the BIOS). Also, many open BIOSes can be customised to meet your machine’s specific needs. If you don’t go the open BIOS route, you can at least configure your BIOS to not search for a floppy drive that’s not there or to boot directly to the first hard drive (instead of the CD drive first). 

 the
the 
 DemocraKey features Clamwin as an
DemocraKey features Clamwin as an 


 (.ppt) and TIFF files (compressed image files) to its services,enabled in Google apps. A few months ago, it had added the support for viewing
(.ppt) and TIFF files (compressed image files) to its services,enabled in Google apps. A few months ago, it had added the support for viewing  Powered up with a richer set of features,the new viewer enables you to zoom in and out, select text to copy and paste, and "print" the presentation to a PDF document. And, unlike the old version, you no longer require to have a Flash plugin installed on your browser.
Powered up with a richer set of features,the new viewer enables you to zoom in and out, select text to copy and paste, and "print" the presentation to a PDF document. And, unlike the old version, you no longer require to have a Flash plugin installed on your browser. postings. From last 1 week,I have been into a cycle of stress and work (cuz I was the organizer of Hacking event in my college and participated in Counter Strike,Crysis,NFS Most Wanted and DOTA all stars,apart from
postings. From last 1 week,I have been into a cycle of stress and work (cuz I was the organizer of Hacking event in my college and participated in Counter Strike,Crysis,NFS Most Wanted and DOTA all stars,apart from 
 sniff out forums and DDL / WAREZ sites for direct links and to get unethical stuff. But as the saying goes,”Give a man a fish and you feed him for a day. Teach a man to fish and you feed him for a lifetime”, after a flurry of emails about on how to crack ftp/pop3/telnet accounts,I decided to post an article on the above stated topic. One of the easy of hacking is brute forcing.You can quickly hack accounts if you have a decent sized password dictionary. I personally use one of about 3.16GB in size, but for this tutorial I'm only going to use a small password list, just so you get the feel of it.
sniff out forums and DDL / WAREZ sites for direct links and to get unethical stuff. But as the saying goes,”Give a man a fish and you feed him for a day. Teach a man to fish and you feed him for a lifetime”, after a flurry of emails about on how to crack ftp/pop3/telnet accounts,I decided to post an article on the above stated topic. One of the easy of hacking is brute forcing.You can quickly hack accounts if you have a decent sized password dictionary. I personally use one of about 3.16GB in size, but for this tutorial I'm only going to use a small password list, just so you get the feel of it.









 may be used illegally by hackers or some other people.Either you may get high internet bills in reward or you may be on headlines as your net may be compromised to send malicious emails to anyone,that's what happened in India sometime ago in Mumbai Bomb blast case. Well,there comes MoocherHunter™ to rescue.
may be used illegally by hackers or some other people.Either you may get high internet bills in reward or you may be on headlines as your net may be compromised to send malicious emails to anyone,that's what happened in India sometime ago in Mumbai Bomb blast case. Well,there comes MoocherHunter™ to rescue.
 available, at least 6 (unwanted) chat
available, at least 6 (unwanted) chat 

 tunnel is an encrypted tunnel created through an SSH protocol connection. SSH tunnels may be used to tunnel unencrypted traffic over a network through an encrypted channel.In easy language,you can surf net without being monitored and even surf blocked sites too.SSH Is pretty awesome.
tunnel is an encrypted tunnel created through an SSH protocol connection. SSH tunnels may be used to tunnel unencrypted traffic over a network through an encrypted channel.In easy language,you can surf net without being monitored and even surf blocked sites too.SSH Is pretty awesome.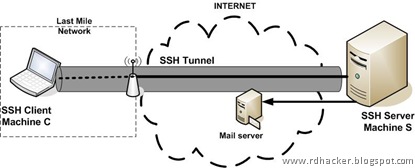 And if you have access to a PC with an SSHd installed, you can channelize your traffic through that computer,which is particularly is useful in situations when -
And if you have access to a PC with an SSHd installed, you can channelize your traffic through that computer,which is particularly is useful in situations when -  channels,one for this website which you can join
channels,one for this website which you can join 


 Congrats,you have created a feed channel for your
Congrats,you have created a feed channel for your 

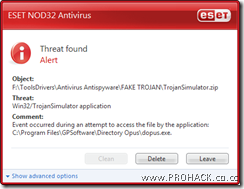
 operating system is getting better each year for desktop and server use. With popularity, however, it has become profitable for thieves to break into
operating system is getting better each year for desktop and server use. With popularity, however, it has become profitable for thieves to break into  christened as
christened as